HCIP-Security V4.0 Exam
Last Update 17 hours ago
Total Questions : 60
HCIP-Security V4.0 Exam is stable now with all latest exam questions are added 17 hours ago. Incorporating H12-725_V4.0 practice exam questions into your study plan is more than just a preparation strategy.
H12-725_V4.0 exam questions often include scenarios and problem-solving exercises that mirror real-world challenges. Working through H12-725_V4.0 dumps allows you to practice pacing yourself, ensuring that you can complete all HCIP-Security V4.0 Exam practice test within the allotted time frame.
In a Huawei network security environment, which of the following is a key advantage of using HWTACACS over RADIUS for device management authentication?
Options:
Predefined URL categories on Huawei firewalls reside in the URL category database delivered with the device and do not need to be manually loaded.
Which of the following statements is false about the ATIC system architecture?
Which of the following statements is false about Eth-Trunk?(Select All that Apply)
The difference between DoS attacks and DDoS attacks is that DoS attacks are usually directly initiated by attackers, whereas DDoS attacks are usually initiated by attackers controlling multiple zombies.
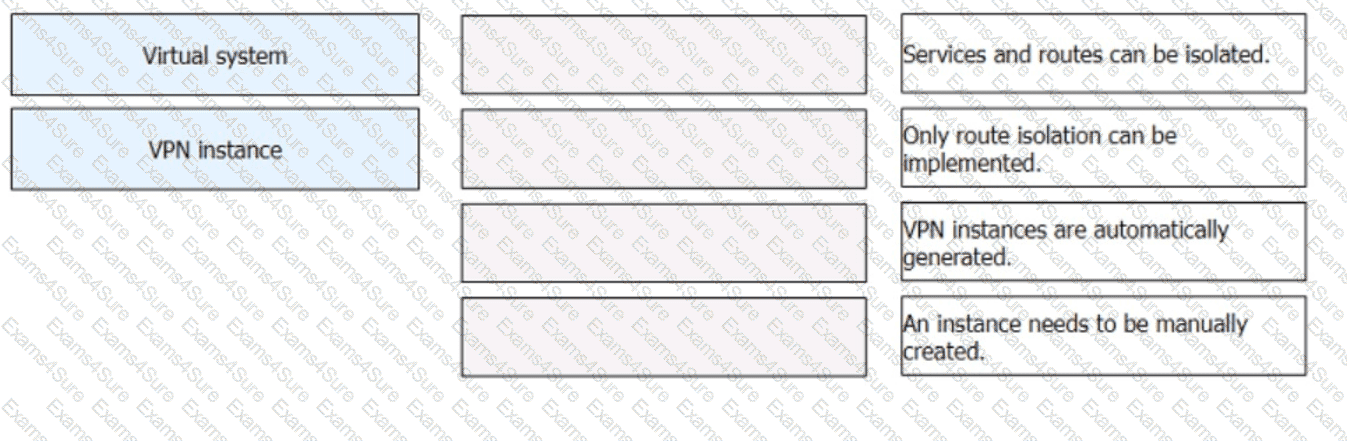
: 51 DRAG DROP
Match the description about virtual systems and VPN instances.
If a Portal authentication user goes offline but neither the access device nor the RADIUS server detects this event, many problems may occur. To prevent this from occurring, the access device needs to detect a user logout immediately, delete the user entry, and instruct the RADIUS server to stop accounting. Which of the following can trigger a Portal user logout?(Select All that Apply)
When Eth-Trunk is deployed for the heartbeat links between firewalls, the Eth-Trunk interface can be configured as a Layer 2 interface as long as the total bandwidth of active links on the Eth-Trunk is greater than 30% of the bandwidth required by service traffic.

TESTED 04 Apr 2025
Hi this is Romona Kearns from Holland and I would like to tell you that I passed my exam with the use of exams4sure dumps. I got same questions in my exam that I prepared from your test engine software. I will recommend your site to all my friends for sure.
Our all material is important and it will be handy for you. If you have short time for exam so, we are sure with the use of it you will pass it easily with good marks. If you will not pass so, you could feel free to claim your refund. We will give 100% money back guarantee if our customers will not satisfy with our products.